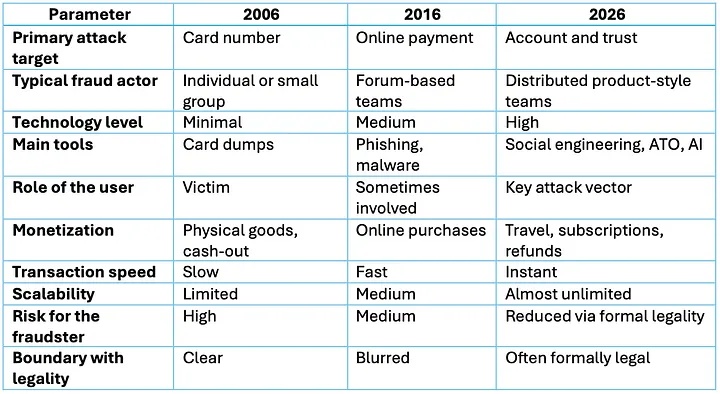
The term carding in 2026 increasingly rarely means the classic picture from the 2000s — stealing card credentials, buying goods, cashing out. The landscape has become much closer to an industry, where profit is generated not only from stolen card numbers, but also from access to user accounts, identity substitution, social engineering, abuse of refunds and disputes, as well as monetization chains through legitimate services. Against the backdrop of growing cashless payments, instant transfers, and ubiquitous online commerce, fraudsters are adapting faster than user habits are changing. European regulators and industry reports directly record growth in damage and a shift of vectors toward manipulation of payers, even in cases where strong authentication continues to operate.
Why carding looks different in 2026
The main change is not that “more cards are being stolen”, but that card data has become only one component of an attack. Strong authentication (SCA, 3DS) and the widespread adoption of tokenization are gradually reducing the value of raw card credentials in scenarios where protection is actually enforced.
This does not mean a decline in fraud. It means migration toward cheaper and more scalable methods — deceiving the user, account compromise, session hijacking, beneficiary substitution, attacks on customer support, attacks on refund and dispute chains. In their recent assessment for the EU/EEA, the ECB and EBA emphasize that the overall volume of payment fraud grew in 2024, and a significant share of new schemes is based on “payer manipulation” and social engineering.
Carding (credit card theft) in 2026 — where criminal activity vectors are shifting
The second change is the development of deception tools and psychological operations. The European ENISA describes the strengthening of social engineering, including the use of AI to scale phishing, content forgery, and personalized scenarios. Even if specific percentages differ across reports, the trend is consensual — persuading and misleading has become easier and cheaper, and attacks can be carried out at scale.
The third change is that money increasingly leaks not through purchases of physical goods, but through digital services and “high-liquidity” assets — tickets, bookings, subscriptions, gift cards, digital codes, marketplaces, taxi services, car sharing, as well as through abuse of refunds and chargebacks. Separately, the importance of the chargeback economy is growing — in some cases it is real fraud, in others friendly fraud, but for businesses the outcome is the same: losses, fees, and the risk of sanctions from payment systems.
Air tickets and travel — why this is still an ideal target
The travel segment, especially air tickets, remains attractive in 2026 for several reasons.
First, it is a high-value product with fast consumption. A fraudster does not need to store or resell a physical good — it is enough for the booking to go through and for the passenger to fly before the transaction can be disputed or stopped.
Second, travel chains are complex: airline, OTA, payment provider, antifraud, customer support, partner programs. Complexity always means more attack surfaces and more places where rules and SLAs can be exploited.
Third, travel is heavily account-driven: personal accounts, saved passengers, documents, loyalty programs, corporate travel accounts. This makes not carding itself but ATO (account takeover) and loyalty theft especially profitable. The airline antifraud market and providers working with the aviation sector note that despite an overall decline in “pressure” from fraud attempts, new hotspots and specific risks remain, including geographic spikes and abuse scenarios.
Key “carding” trends of 2026, if we speak honestly
A map of tendencies used by banks, merchants, and antifraud teams to plan defenses.
• Shift from stealing credentials to stealing identity and account control: compromise of email, phone numbers, messengers, account recovery via support, session hijacking, device substitution.
• Growth of social engineering as the main entry point: fake “security services”, “payment confirmations”, “refunds”, “delivery checks”, “debts”, “fines”, “KYC updates”. In its threat review, EPC explicitly highlights social engineering and related payment fraud enablers.
• Scaling phishing and deception using AI — more convincing texts, localization by language and country, voice and video deepfakes in targeted attacks against support or employees. ENISA.
• Commercialization of dispute abuse: fraudsters play not only on successful charges, but also on refunds, cancellations, promotional terms, bonuses, “service not received”. This is already an intersection zone between fraud and customer operations, and it strongly affects the financial model.
• Shift toward “digital liquidity” — travel, gift cards, subscriptions, digital goods, instant-consumption services. Travel remains at the top precisely as a fast and expensive asset.
• Pressure on instant payments and transfers: where money leaves irreversibly, the value of deceiving the payer and substituting details grows, rather than compromising cards. ECB/EBA note that in terms of value, a significant share comes from credit transfers and card payments, reflecting the overall shift from “card as the only instrument” to broader payment fraud.
Normalization of tokenization and mobile wallets: for attackers this means that “raw card data” is monetized worse where tokens and strong authentication are truly enabled, while the value of account and device takeover grows.
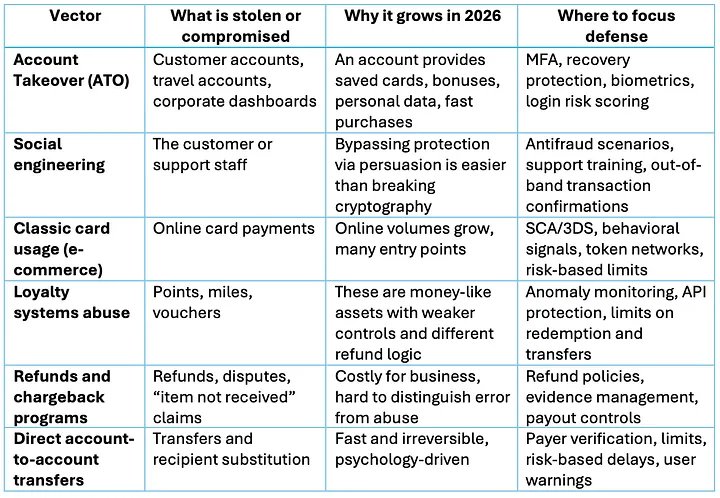
What is attacked in 2026 and how it looks for business
There are deliberately no “hacking techniques” in the table: in 2026, the winner is not the one who knows a single trick, but the one who builds defense as a chain of processes and closes the most profitable points.
Carding (credit card theft) in 2026 — where criminal activity vectors are shifting
United States — a hybrid of technology, legality, and abuse
The picture in the US is different, but the evolution is the same. A huge market, a high share of credit cards, a developed chargeback culture, and softer consumer protection have created a unique environment where the boundary between fraud and abuse is blurred.
By 2026, the American “carder” is increasingly less associated with the illegal card market. Much more often, this is:
• an account takeover specialist,
• a refund abuse operator,
• a participant in friendly fraud schemes,
• an abuser of promos, trials, and subscriptions,
• a player exploiting weaknesses in dispute systems.
The US specialty is monetization through legal mechanisms. Refunds, cancellations, “item not received”, “service not provided”, disputes with banks. In travel and subscription services this is especially visible. Air tickets, hotels, car rentals, streaming — all become part of gray schemes where formally the user “defends their rights”, but in practice systematically extracts money.
The American ecosystem produces a technologically literate fraudster who:
• knows Visa and Mastercard rules,
• understands how customer support works,
• uses legitimate APIs and interfaces,
• automates disputes and refunds,
• rarely steals a card directly, but often controls the account.
Carding in 2026 is no longer so much a story about “stealing a card”, but about managing trust — who is authorized, who makes the decision, who controls the account, how refunds are structured, and how quickly a digital operation can be converted into real value.
Air tickets and travel remain on the front line not because of romance, but because of economics: high value, fast realization, complex chains, and many accounts.
By 2026, carding has evolved from ‘card theft’ into a complex industry of user manipulation and control over digital identities.
