The validity period of documents in Connecticut depends on their type. The state is now switching to longer validity periods...
21.04.2026
0

The Arizona DL (Arizona Driver’s License) version dated 02/14/2014 refers to the design introduced by ADOT. These cards included enhanced...
13.04.2026
0

In Arizona, a driver’s License (DL) is issued for a very long time, one of the longest in the United...
07.04.2026
0

These days, when online privacy’s gettin’ more valuable—and at the same time more bloody vulnerable—tech for anonymisin’ and encryptin’ traffic...
01.04.2026
0

There’s a name currently circulating in cybersecurity discussions across Nigeria: ByteToBreach. The group (or individual) has claimed responsibility for two...
01.04.2026
0
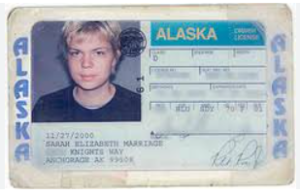
Driver’s Licenses (DL) in Alaska are usually issued for a period of up to 5 years, with the validity period...
31.03.2026
1

Every day, millions of people paste emails, code snippets, internal documents, and personal information into ChatGPT, Gemini, and Claude without...
31.03.2026
0

Bug bounty hunting is not just about luck. It’s about having a repeatable system. Most beginners jump from one tool...
31.03.2026
0

Ali was doing what thousands of freelancers do every day—juggling clients, deadlines, and tools to stay productive. His browser was...
31.03.2026
0